How To Set Up Password In Windows 7
In Role 2 of our series on Microsoft LAPS (Local Administrator Password Solution), I'll show you how to update your Active Directory schema to support LAPS and configure permissions for both computers and admins.
- Writer
- Recent Posts
![]()
To set up the Microsoft Local Administrator Password Solution (LAPS) in Active Directory, yous'll start demand to download LAPS from the Microsoft Download Center. You lot'll want to download both the LAPS.x86.msi (for 32-chip systems) and LAPS.x64.msi (for 64-bit systems).
On my domain controller, I'm going to run the 64-bit installer, LAPS.x64.msi. After clicking Next for the starting time ii screens and accepting the license agreement, you'll need to ensure that the Management Tools (but non the AdmPwd GPO Extension) are prepare to install on the server.
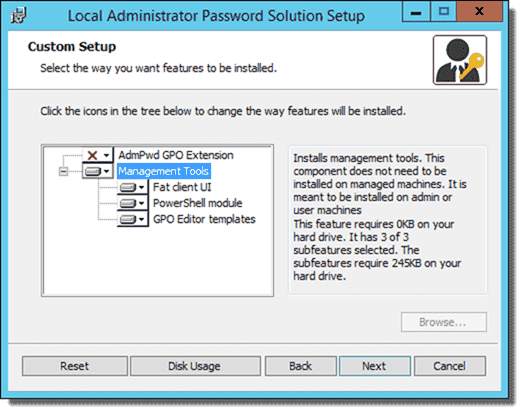
Local Administrator Countersign Solution custom setup options for server
After a few more Next clicks, the LAPS direction tools are installed on the server. If y'all go to the Start screen, you should meet the new LAPS UI, which I'll cover a little later.

LAPS UI on Commencement screen
Adjacent, we'll demand to open a PowerShell window with Admin rights. At the PowerShell prompt, load the LAPS module and and then run the Update-AdmPwdADSchema cmdlet:
Import-Module AdmPwd.PS Update-AdmPwdADSchema
When you're done running the commands, you should get three "Success" messages:
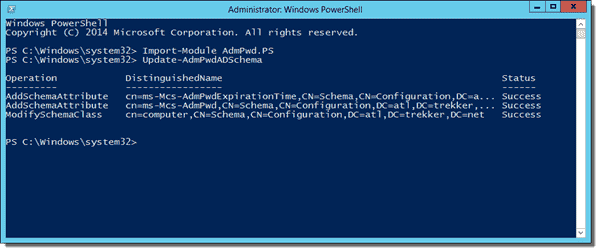
Extending the Active Directory Schema to support LAPS
Update user/group AD permissions ^
After updating the Agile Directory schema, nosotros need to check permissions in AD to ensure that just authorized users and groups can view the passwords that are stored there. By default, Domain Admins and Enterprise Admins volition accept admission to view the stored passwords, along with any other groups or users y'all've delegated. First, open up a PowerShell window and ensure that the AdmPwd.PS module is loaded. We can so use the Find-AdmPwdExtendedRights cmdlet to view which users and groups have admission to view stored passwords:
Import-Module AdmPwd.PS Find-AdmPwdExtendedRights –Identity "_Demos"
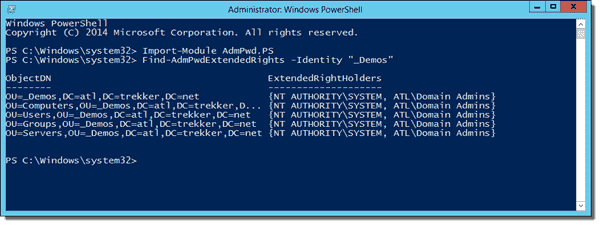
Find-AdmPwdExtendedRights output example
As you can meet in the screenshot to a higher place, I don't accept any users that shouldn't have admission in my AD environs. If you do have users that shouldn't be able to view the stored password data that bear witness up in "ExtendedRightHolders," yous'll demand to remove their admission to "All extended rights." In Active Directory Users and Computers (ADUC), click View and ensure that y'all accept Advanced Features checked. Right-click the OU proper name and then click Properties, Security, and Advanced.

Editing avant-garde permissions in Active Directory Users and Computers
Side by side, select the group (or user) that should not accept access to view the managed Ambassador passwords and click Edit. Articulate the All extended rights check box. Click OK twice to save the change.
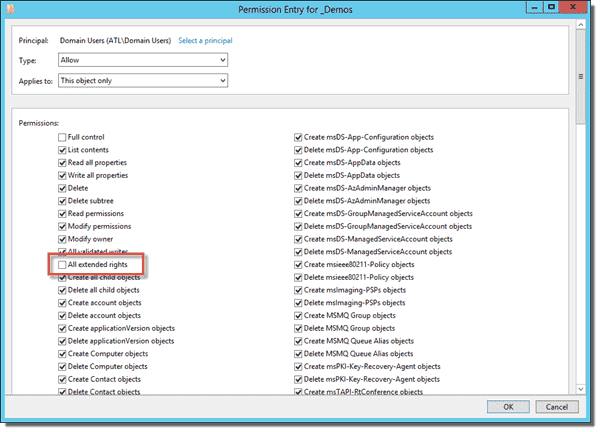
Removing access to all extended rights
If y'all want to give additional groups access to view the passwords, you tin use the Set-AdmPwdReadPasswordPermission cmdlet to give users or groups the ability to read the attributes:
Import-Module AdmPwd.PS Set-AdmPwdReadPasswordPermission –Identity "_Demos" –AllowedPrincipals "Help Desk"
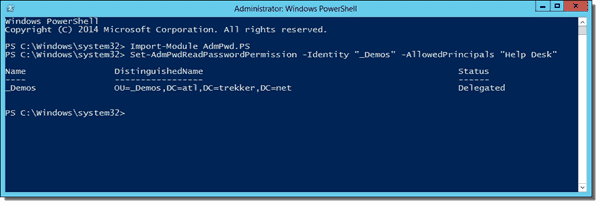
Using Set-AdmPwdReadPasswordPermission to delegate additional groups
Update estimator Ad permission ^
Last, we'll need to give the computers the ability to update the ms-Mcs-AdmPwd and ms-Mcs-AdmPwdExpirationTime attributes in Active Directory. Start by loading the module again (if you don't already have it loaded) and running Set up-AdmPwdComputerSelfPermission:
Import-Module AdmPwd.PS Fix-AdmPwdComputerSelfPermission –Identity "_Demos"
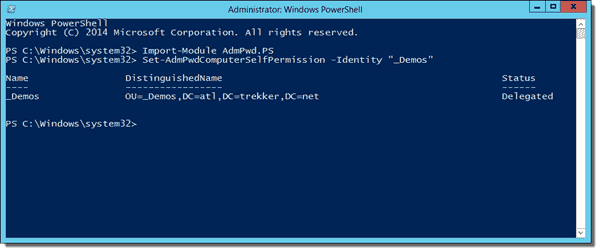
Using Fix-AdmPwdComputerSelfPermission to give computers write access to passwords
You'll need to run this for each OU that will have managed computers but not the sub-OUs because the new permissions will apply to the sub-OUs.
At this point, our Active Directory infrastructure is configured to support the new Active Directory attributes and permissions for those attributes. In the terminal role of this series, I'll encompass setting upward the clients and configuring the Group Policy for LAPS.
How To Set Up Password In Windows 7,
Source: https://4sysops.com/archives/set-up-microsoft-laps-local-administrator-password-solution-in-active-directory/
Posted by: wanniong1966.blogspot.com


0 Response to "How To Set Up Password In Windows 7"
Post a Comment